Running ZK-proven Queries
Get started running tamperproof queries with Proof of SQL℠!
The <Glossary>Space and Time Database</Glossary> allows users to run tamperproof queries that use ZK cryptography to generate a proof that ensures neither the SQL nor the data have been tampered with. You can have that proof immediately applied within the <Glossary>SxT</Glossary> network, or send it to another third-party verifiers, allowing you to extend the zero-trust model of a blockchain into a big-data system.
Automated Verification
Running a tamperproof query is surprisingly simple - you only need a <Glossary>Space and Time</Glossary> account, a tamperproof table, and a verifier.
<Glossary>Native Verification</Glossary> with Space and Time Studio
The easiest way to run a tamperproof query is using <Glossary>Space and Time Studio</Glossary>, as it provides a seamless and unified experience.
Step 1: Login to Space and Time Studio
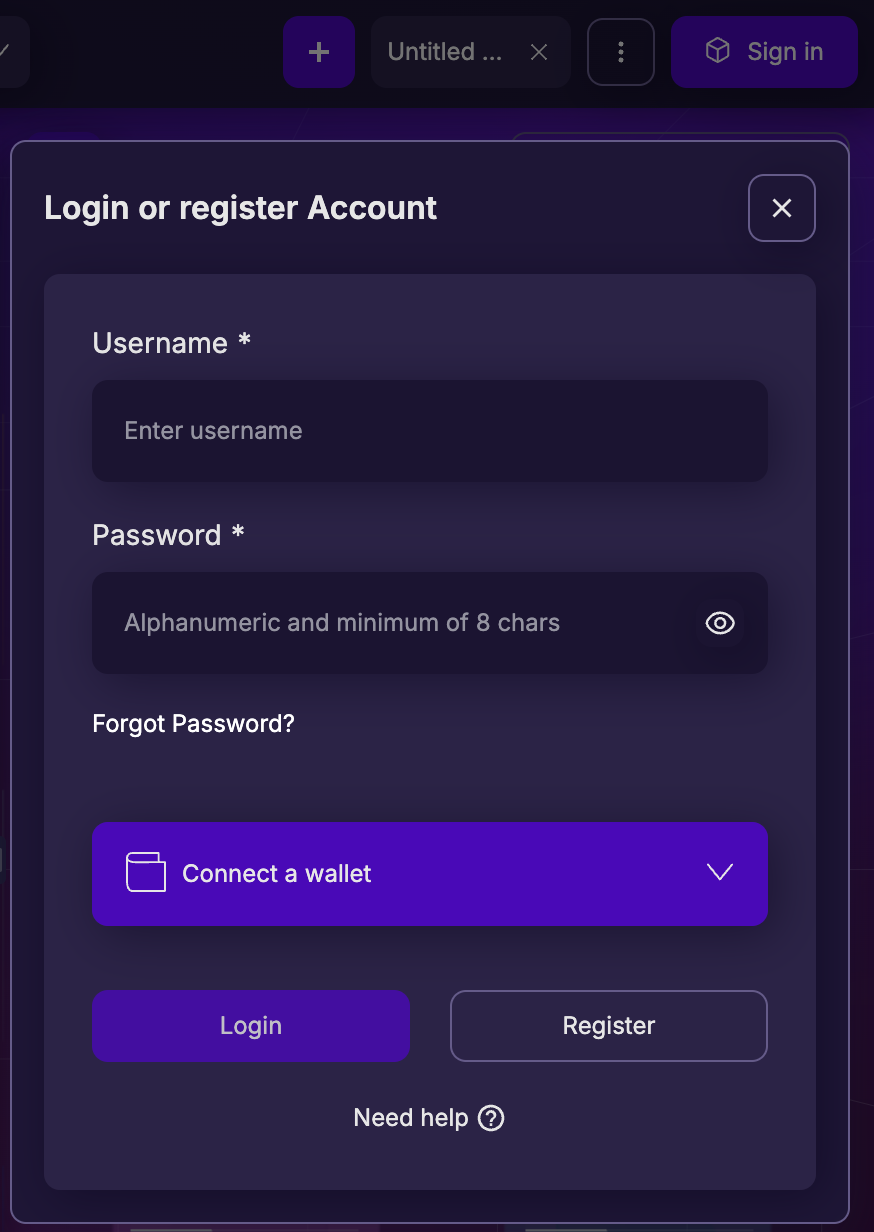
To login to Space and Time Studio dapp:
Navigate to the Space and Time Studio dapp and click on "Sign in" in the upper-right most corner.
Enter your Username and Password, and click "Login"
OR
Click the "Connect a wallet" button at the bottom, and use your wallet to sign into your Space and Time account.
Once authenticated, you should see the "Sign in" button replaced by a "My account" button in the upper right, where you can manage your account and subscription settings.
🔥 New User? Click here to create an account! 🔥
Step 2: Run a Tamperproof Query
Once logged in to Space and Time Studio, you can run a tamperproof query directly in the query editor:
- Click on the "Queries" menu tab, to pull up the "Query Editor"
- In the main query editor space, click on the Proof of SQL button (looks like a database with a key) to the immediate left of the "Run Query" button - this will open a pop-out box
- At the top of that pop-out next to the "Proof of SQL" title, click the toggle switch so that it reads "ENABLED" (this will also add a small green indicator to the Proof of SQL button)
- Click the "Run Query" button!
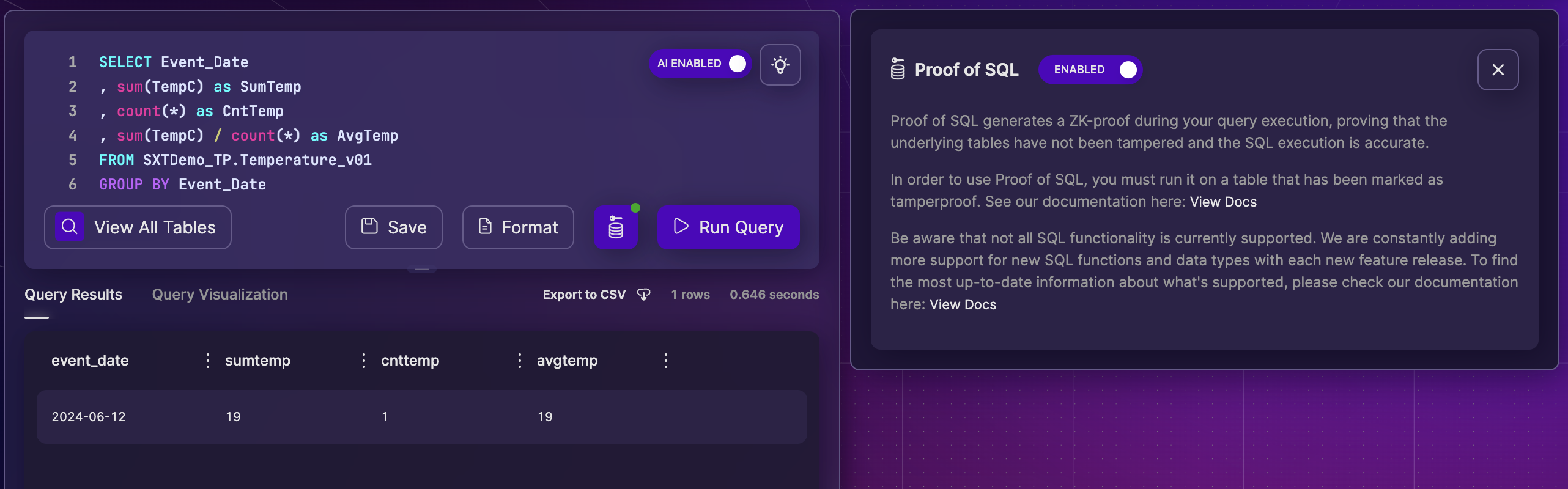
If you would like to follow-along with the SQL above:
SELECT Event_Date
, sum(TempC) as SumTemp
, count(*) as CntTemp
FROM SXTDemo_TP.Temperature_v01
GROUP BY Event_DateA script to create the tamperproof table above can be found in the recipe, "Create a Tamperproof Table.
Contrats, you've run a tamperproof query! All queries submitted through the "Query Editor" will now also generate a ZK proof, and be verified using the SxT verifier network.
<Glossary>Native Verification</Glossary> with Space and Time API
If you interface with the <Glossary>Space and Time Database</Glossary> using APIs and you want to run <Glossary>Native Verification</Glossary>, the change is as easy as using a different, but identical, SQL API endpoint.
To keep examples OS and programming language agnostic, the example below uses the SXT CLI in a <Glossary>terminal</Glossary> window.
Step 1: Install SXT CLI
If not already complete, follow these instructions to install the Space and Time CLI.
Step 2: Login to Space and Time
To login to the Space and Time network using the CLI, make sure you've installed the Space and Time CLI and have a valid space and time user, then copy/paste the commands below into a terminal:
- Replace placeholders below with your credentials and copy/paste the below SXTCLI command into a terminal:
sxtcli authenticate login \
--url="https://api.spaceandtime.dev" \
--userId="your_userid" \
--publicKey="your_public_key" \
--privateKey="your_private_key"API_URL="https://api.spaceandtime.dev"
USERID="your_userid"
USER_PUBLIC_KEY="your-public-key"
USER_PRIVATE_KEY="your-private-key"
sxtcli authenticate login \
--url=$API_URL \
--userId=$USERID \
--publicKey=$USER_PUBLIC_KEY \
--privateKey=$USER_PRIVATE_KEYThis command will return two tokens:
- ACCESS_TOKEN - used to authenticate any API calls to the network, expires after 25 minutes
- REFRESH_TOKEN - used to request a new ACCESS_TOKEN, expires after 30 minutes
An ACCESS_TOKEN is an authenticated session to the Space and Time network - to keep yourself secure, please treat your ACCESS_TOKEN as a secure key and do not share with others.
- Optionally, it's a good idea to copy the ACCESS_TOKEN to an environment variable. This can be done manually, i.e.,
ACCESS_TOKEN="eyJ0eXBlIjoiY..."or if on Linux / MacOS, by directing the CLI output to a parser likeawk:
ACCESS_TOKEN=$( \
sxtcli authenticate login \
--url="https://api.spaceandtime.dev" \
--userId="your_userid" \
--publicKey="your_public_key" \
--privateKey="your_private_key"
| awk 'NR==2{ print $2 }' )API_URL="https://api.spaceandtime.dev"
USERID="your_userid"
USER_PUBLIC_KEY="your-public-key"
USER_PRIVATE_KEY="your-private-key"
ACCESS_TOKEN=$( \
sxtcli authenticate login \
--url=$API_URL \
--userId=$USERID \
--publicKey=$USER_PUBLIC_KEY \
--privateKey=$USER_PRIVATE_KEY
| awk 'NR==2{ print $2 }' )- Optionally, let's test our ACCESS_TOKEN by submitting a request to the network. Assuming your ACCESS_TOKEN is stored in an environment variable as described above, you can request details on your UserID, or run queries.
curl --request POST \
--url "https://api.spaceandtime.app/v1/sql" \
--header "accept: application/json" \
--header "authorization: Bearer $ACCESS_TOKEN" \
--header "content-type: application/json" \
--data '{
"sqlText": "Select count(*) as Blocks_Yesterday from Ethereum.Blocks where time_stamp between current_date-1 and current_date"
}'curl --request GET \
--url https://api.spaceandtime.app/v1/auth/validtoken \
--header 'accept: application/json' \
--header "authorization: Bearer $ACCESS_TOKEN"Contrats, you've authenticated to the Space and Time network and generated an ACCESS_TOKEN using the CLI!
Hint: If you plan to use the CLI frequently, you might consider:
- It's a best practice to store user secrets in a dotenv (.env) file
- Check out this this community project for CLI shortcuts
Step 3: Run a Tamperproof Query
Running a natively verified tamperproof query using the API is nearly identical to running a normal SQL query request, except using the tamperproof SQL API endpoint. Using this API will generate the query results, the ZK Proof, and use the SxT verifier network to perform the verification - all automatically in one step!
To run a query using the CLI, open a terminal window, log into the Space and Time network to get an ACCESS_TOKEN, saved to an environment variable ACCESS_TOKEN, and then submit the API call:
SQL="SELECT Event_Date, sum(TempC) as SumTemp, count(*) as CntTemp FROM SXTDemo_TP.Temperature_v01 GROUP BY Event_Date"
curl --request POST \
--url https://api.spaceandtime.app/v2/sql/tamperproof-query \
--header 'content-type: application/json' \
--header "authorization: Bearer $ACCESS_TOKEN" \
--data '{ "sqlText": "'"$SQL"'" }'Contrats, you've run a tamperproof query!
Optionally, let's run the same query above but using the normal SQL endpoint. The query result is the same, but note that you'll get MORE information back from the tamperproof endpoint than you will from the normal endpoint. This is because the tamperproof endpoint will include, among other metadata information, the verification hash. The endpoint signature between the two is identical, except for the URL:
SQL="SELECT Event_Date, sum(TempC) as SumTemp, count(*) as CntTemp FROM SXTDemo_TP.Temperature_v01 GROUP BY Event_Date"
curl --request POST \
--url https://api.spaceandtime.app/v1/sql \
--header 'content-type: application/json' \
--header "authorization: Bearer $ACCESS_TOKEN" \
--data '{ "sqlText": "'"$SQL"'" }'Other Ways to Verify
Run Your Own Verifier
<Glossary>Space and Time</Glossary> has open-source the verifier code, meaning for centralized use-cases you can install and perform local verification. This is great for any use-case where you alone need to verify the proof, such as internal analytics, centralized transactions, or fully internal work not shared with 3rd parties (or those parties trust you to perform the work correctly).
To get started with your own verifier, simply clone the Proof of SQL Verifier repo, located here:
https://github.com/spaceandtimelabs/SXT-proof-of-sql
Coming Soon! Verify with Partners (like Chainlink)
<Glossary>Space and Time</Glossary> is partnering with ZK verifier networks to broaden the choice of decentralized, 3rd party verifiers for your proofs. These will be coming online over the course of the next few months, so check back frequently for the growing list!
Coming Soon! Verify On-Chain
<Glossary>Space and Time</Glossary> cryptography teams are working hard to hyper-optimize the verifier to run onchain efficiently enough to be financially practical, even for high-cost / settlement chains. Look for this coming soon!
Ready to Build Your Own Tables / Queries?Check out this page, where you can read up on currently available Proof of SQL syntax and learn tamperproof table best practices!
Updated 6 months ago